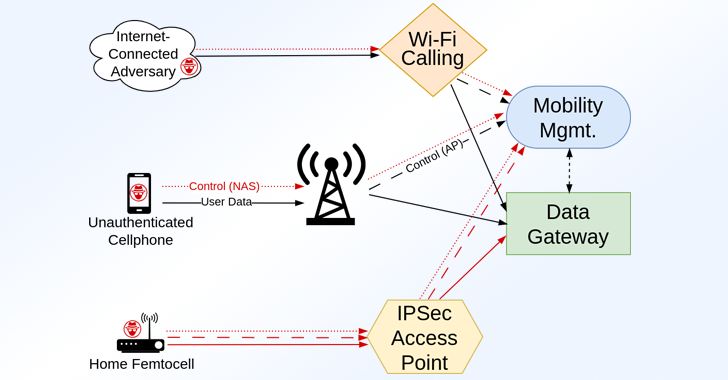
Ransomware Targets ESXi Systems via Stealthy SSH Tunnels for C2 Operations
Cybersecurity researchers have found that ransomware attacks targeting ESXi systems are also leveraging the access to repurpose the appliances as a conduit to tunnel traffic to command-and-control (C2) infrastructure and… Read More »Ransomware Targets ESXi Systems via Stealthy SSH Tunnels for C2 Operations