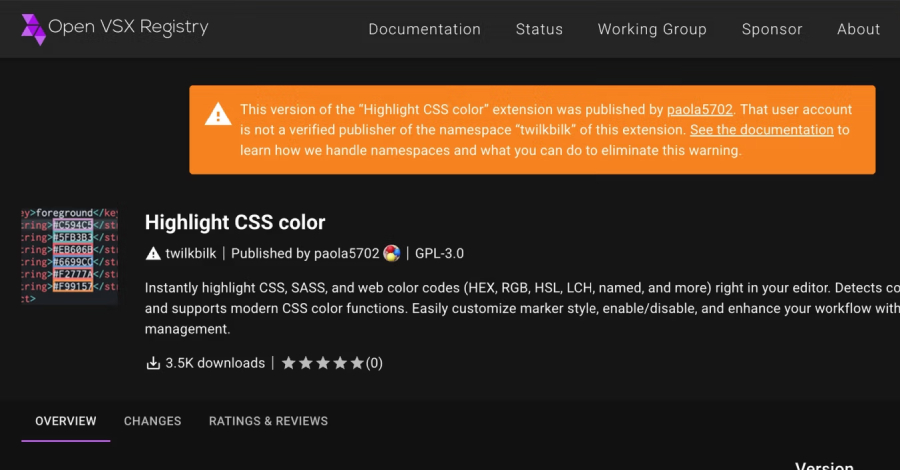
Cybersecurity researchers have flagged a new iteration of the GlassWorm campaign that they say represents a “significant escalation” in how it propagates through the Open VSX registry.
“Instead of requiring every malicious listing to embed the loader directly, the threat actor is now abusing extensionPack and extensionDependencies to turn initially standalone-looking extensions into transitive Cybersecurity researchers have flagged a new iteration of the GlassWorm campaign that they say represents a “significant escalation” in how it propagates through the Open VSX registry.
“Instead of requiring every malicious listing to embed the loader directly, the threat actor is now abusing extensionPack and extensionDependencies to turn initially standalone-looking extensions into transitive The Hacker News